The latest weekly report is out and in the AUCloud Cyber Threat Intelligence Report we reveal:
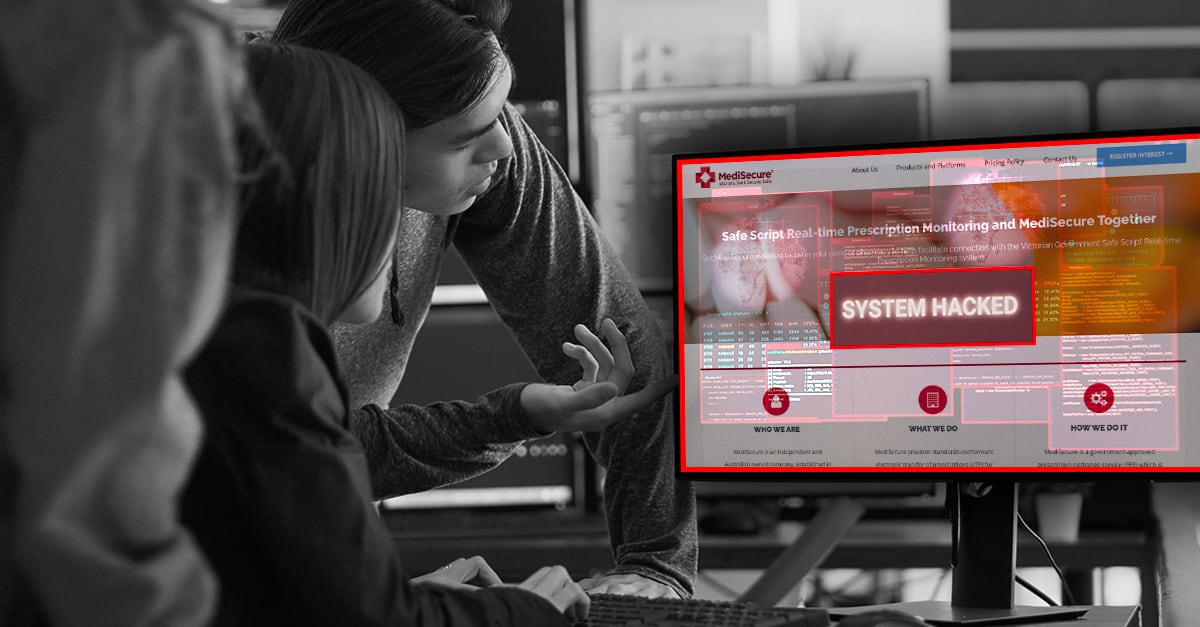
MediSecure e-script firm hit by ‘large-scale’ ransomware data breach
MediSecure, an electronic prescription provider in Australia, has been significantly impacted by a ransomware attack believed to have originated from a third-party vendor. The attack has prompted the company to shut down its website and phone lines as it assesses the extent of the data breach, which has affected the personal and health information of numerous individuals.
Critical flaw in AI Python package can lead to system and data compromise
A critical vulnerability, CVE-2024-34359, named “Llama Drama,” has been discovered in the Python package llama_cpp_python, widely used by AI application developers, posing significant risks to systems and data. Identified by researcher Patrick Peng, this flaw involves the Jinja2 template rendering tool and allows for arbitrary code execution due to improper security measures, such as the lack of sandboxing during template processing.
China-linked hackers adopt two-stage infection tactic to deploy Deuterbear RAT
Cybersecurity researchers have uncovered that the China-linked BlackTech group is using a sophisticated two-stage infection tactic with a remote access trojan (RAT) named Deuterbear in cyber espionage campaigns targeting the Asia-Pacific region. This advanced malware, a successor to Waterbear, evades detection by using shellcode plugins and HTTPS for command-and-control communication.
Cyber criminals exploit Github and Filezilla to deliver malware cocktail
Cybercriminals have found a new avenue to distribute malware by exploiting GitHub and other DevOps tools. They utilize GitHub’s file upload feature within comments to distribute malicious files under the guise of legitimate projects, making them appear as if they are hosted by trustworthy repositories such as Microsoft’s. This technique takes advantage of GitHub’s structure, where files attached to comments generate URLs linked to the project, thereby making the malware distribution seem credible and bypassing many security defenses.
Access to the full report and automatically subscribe for future editions.